- Posted on April 22, 2026
- 14 Min Read
Passwords are the first line of defense for every team, yet they are also one of the most common sources of security risk. A zero knowledge password manager is designed to solve this problem by ensuring that only the user can access their stored credentials.
Even the service provider cannot see or read the data. This approach adds a strong layer of privacy and control, which is critical for teams that handle sensitive information every day.
In this blog, you will learn what a zero knowledge password manager really means, how it works behind the scenes, and why it matters for modern teams. It will also explain how this model reduces internal and external risks, supports secure collaboration, and helps organizations stay compliant with data protection standards.
The need for stronger password security is clear. According to its 2024 Password Manager Report, only 36 percent of adults use a password manager, while over half still rely on unsafe methods like memorization or written notes. This shows how important it is to move beyond traditional password storage methods and adopt systems that do not expose sensitive data at any point.
By the end of this blog, you will have a clear understanding of why zero knowledge architecture is becoming essential for teams and how it can strengthen your overall security strategy.
What is zero-knowledge in a password manager?
A zero-knowledge password manager encrypts your vault on your device before any data reaches the provider’s servers. The provider stores only ciphertext never your master password, never your encryption key. Even if the company is breached or subpoenaed, your credentials cannot be read by anyone without your key.
The term gets thrown around in a lot of password manager marketing, which is precisely why it’s worth understanding what it actually requires. Standard encryption protects your data in transit and at rest, but the provider may still hold the decryption keys, which means they could read your data if compelled to, or if their key management is compromised. Zero-knowledge removes the provider from the key equation entirely.
In practice, it works in three steps:
- Encryption on your device. Your vault data is encrypted locally, in your browser or app before it goes anywhere.
- Only ciphertext leaves your device. The encrypted blob is what travels to the server. Unreadable without your key.
- Decryption on your device. When you open your vault, the ciphertext comes back and is decrypted locally. The server never sees plaintext.
Your master password never leaves your device. The server stores a cryptographic proof that you know the correct password, enough to verify your identity, but not the password itself and not the derived encryption key.
Zero-knowledge is a spectrum, not a binary certification. A provider can implement client-side encryption for vault contents but still retain unencrypted metadata, URL entries, timestamps, vault item counts.
A USENIX Security ’26 paper analysing cloud-based password managers found design anti-patterns in some products’ ZK claims. When evaluating the right password manager, ask specifically what is and is not covered by their zero-knowledge model.
How All Pass Hub implements zero-knowledge encryption
Most password managers that claim zero-knowledge describe the concept without disclosing the technical specifics. Here is All Pass Hub’s implementation stack in full, the kind of detail that lets you verify the claim rather than take it on faith.
| Layer | Implementation | What it means |
|---|---|---|
| Vault encryption | AES-128 | Your vault data is encrypted using AES-128 (Advanced Encryption Standard with a 128-bit key). This cipher has no known practical attack at current computing capability. |
| Key derivation | PBKDF2-SHA256, 600,000 iterations | PBKDF2 (Password-Based Key Derivation Function 2) converts your master password into an encryption key by running it through SHA-256 hashing 600,000 times. This makes brute-force guessing computationally expensive. NIST recommends a minimum of 600,000 iterations as of 2023. |
| Shared vault key exchange | RSA-based key exchange | When you share access to a vault with a team member, RSA (an asymmetric encryption algorithm) is used to securely wrap the vault key for each recipient. The server facilitates the exchange without ever receiving the plaintext vault key. |
| Encryption location | Client-side (browser / app) | All encryption and decryption happens on your device. The All Pass Hub server receives and stores ciphertext only. |
What this means in a breach scenario: if All Pass Hub’s servers were compromised tomorrow, an attacker would retrieve an encrypted blob that is computationally unreadable without each user’s master password and derived key. There is no server-side key to steal because one does not exist.
A note on AES-128 vs AES-256. AES-128 and AES-256 differ in key size (128-bit vs 256-bit). Both are considered secure against current and near-future attacks which means no practical attack exists against either.
However, some compliance frameworks (FedRAMP, certain ISO 27001 auditors) specifically require AES-256. If your organisation operates under one of these frameworks, verify this detail with All Pass Hub before committing.
Is All Pass Hub zero-knowledge?
Yes. All Pass Hub is designed around a zero-knowledge architecture, which means your sensitive data is encrypted before it ever leaves your device. Only you and the people you explicitly grant access to can decrypt that data. The platform does not have access to your plaintext passwords, encryption keys, or vault contents.
All Pass Hub uses strong encryption standards and a secure key management approach to ensure that credentials remain protected at all times. Its use of RSA-based key exchange enables secure sharing between users while preserving the zero-knowledge model. This is particularly important in team environments where credentials need to be accessed by multiple people without exposing the underlying data.
Unlike many password managers that were originally built for individual use, All Pass Hub is structured specifically for teams. This allows it to handle shared access, role-based permissions, and user lifecycle management in a way that aligns with how organisations actually operate.
For comparison, Bitwarden also follows a zero-knowledge model and is widely respected for its security practices, including client-side encryption and open-source transparency. Bitwarden encrypts vault data client-side using AES-256 and derives encryption keys from your master password using PBKDF2.
Bitwarden’s servers never receive your plaintext passwords or your encryption key. Bitwarden has also published a detailed white paper defining the scope of their zero-knowledge model, including a pointed acknowledgement that some unnamed competitors retain unencrypted URL data, giving those providers detailed records of which sites users visit. Bitwarden encrypts URLs within the vault.
Bitwarden is also open-source. That means their zero-knowledge implementation can be and has been independently audited, not just claimed. For a security-sensitive purchase, that is a genuine differentiator worth acknowledging. It is a strong choice for individuals and for teams that are comfortable adapting an individual-first vault structure to collaborative use.
The key difference lies in design focus. All Pass Hub approaches zero-knowledge with team workflows as a core requirement, not an extension. This makes it a practical option for organisations that need secure credential sharing, structured access control, and efficient onboarding and offboarding without compromising on security.
Also Read – Bitwarden vs All Pass Hub — Which Password Manager Is Right for Your Team?
Which password managers are truly zero-knowledge?
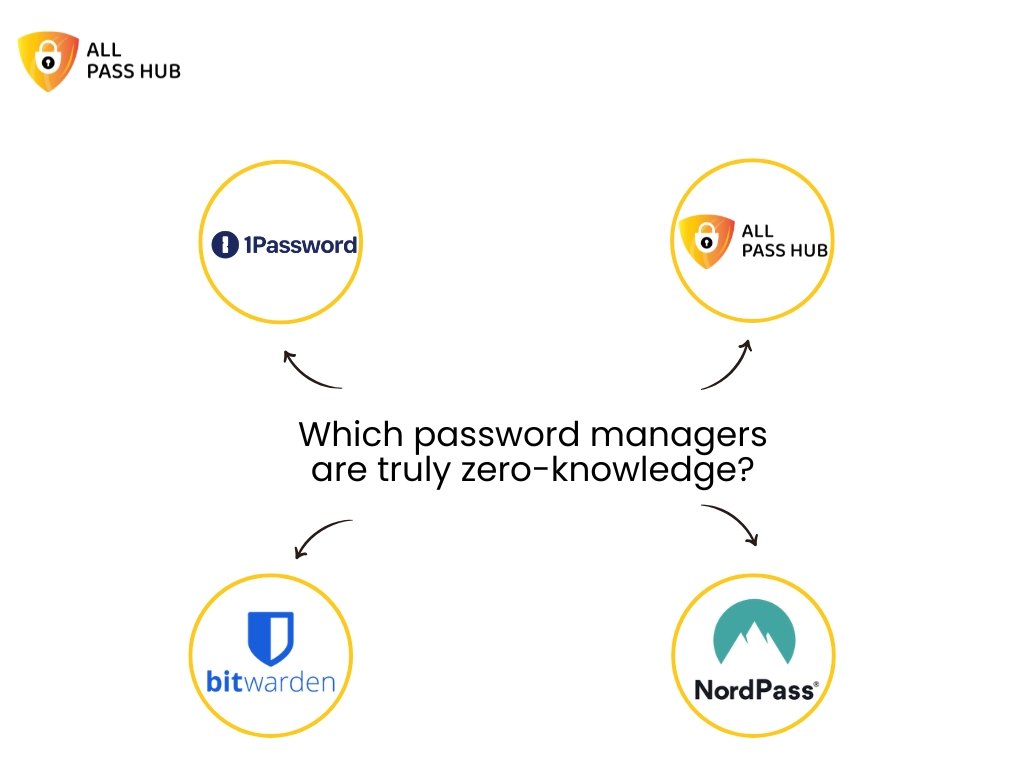
Before the list: “truly zero-knowledge” is not a certified standard. It is a design claim, one that is only as reliable as a vendor’s published documentation and, ideally, independent audit. The USENIX Security ’26 paper on cloud-based password managers found design vulnerabilities in some products that marketed themselves as zero-knowledge. That paper is worth reading if you are making a security-sensitive purchasing decision.
With that caveat stated, the following managers have documented client-side encryption and no server-side key access, based on available published evidence.
Evaluation criteria used:
(1) client-side encryption confirmed,
(2) master password never transmitted to the server,
(3) key derivation function with sufficient iteration count,
(4) no unencrypted metadata retention.
- All Pass Hub – AES-128 client-side encryption, PBKDF2-SHA256 with 600,000 iterations, RSA-based key exchange for shared team vaults. Designed natively for multi-user credential sharing while preserving zero-knowledge throughout.
- Bitwarden – AES-256 client-side encryption, PBKDF2 key derivation, open-source and independently audited. Encrypts vault URLs. Particularly strong for individual users and self-hosted environments.
- 1Password – Zero-knowledge encryption with account passwords never sent over the network. Uses a Secret Key model (a locally-stored key combined with your master password) for additional protection.
- NordPass – All encryption and decryption occurs on the user’s device before backup and sync. Master password not stored by NordPass.
When evaluating any tool on this list, ask one additional question: does the provider encrypt vault metadata, specifically, the URLs of sites for which you store credentials? Some providers retain these unencrypted. For most teams this is a low-risk detail; for teams handling sensitive client credentials, it matters.
Also Read – The Small Agency Password Playbook: Practical Steps to Strengthen Security in 2026
Does zero-knowledge mean the company can’t access my passwords?
Yes, in a properly implemented zero-knowledge model, the answer to this question is an unambiguous yes. The company cannot read your vault contents. It does not matter if they want to, if they are audited, or if a government issues a lawful request for your data. Without your encryption key, the data is ciphertext. They cannot produce what they do not hold.
ZK protects against
- Server-side data breaches
- Insider threats and rogue employees
- Subpoenas for vault contents
- Provider infrastructure compromise
ZK does not protect against
- A compromised device or browser extension
- A weak master password (brute-forceable)
- Unencrypted metadata (URLs, timestamps) if retained
- User error — phishing, for example
There is one important implication that catches teams off guard: account recovery. Because the provider does not store your master password, they cannot reset your vault if you forget it. Most zero-knowledge managers handle this by generating an emergency access kit or recovery code at account creation, a one-time credential you store offline. If you lose both your master password and your recovery code, the vault contents are unrecoverable by design.
For All Pass Hub specifically, users should generate and store their recovery code at account setup. IT administrators managing a team account should treat this code with the same care as any other critical offline credential, ideally stored in a physical safe or an offline secrets manager.
Zero-knowledge is not a guarantee of perfect security. It eliminates one class of risk provider access to your vault but your data is only as secure as the device it lives on, the master password protecting it, and the practices of the people who have access to it.
Also Read – Password Security for Agencies: Why Ignoring It Could Cost You Everything
Why zero-knowledge architecture matters specifically for teams
Most zero-knowledge explainers are written for a single user with a personal vault. The team context introduces three scenarios that the single-user model does not have to solve and where the architecture matters far more than the marketing.
1. Sharing without exposing
When you share a vault credential with a colleague, the encryption model faces a challenge: the server needs to facilitate the exchange without ever receiving a plaintext key. All Pass Hub’s RSA-based key exchange solves this. Each team member holds their own keypair; when a vault item is shared, the item key is wrapped (encrypted) using the recipient’s public key. The server passes the encrypted package but never sees its contents. Zero-knowledge is preserved through the share event, not just within individual vaults.
2. Offboarding that actually works
When a team member leaves, revoking their vault access is only meaningful if the access was genuine and localised. In a zero-knowledge model, the departing employee never held server-side keys, only their own local keypair and the vault items explicitly shared with them. Revoking their access removes their ability to decrypt those items going forward. There is no risk that a compromised server credential gives them continued read access, because the server never held decryptable data in the first place.
3. Admin logs without admin access
A common misconception is that audit logging is incompatible with zero-knowledge that if an admin can see who accessed what, the admin must be able to see the contents. This is not the case. Audit logs record access events (which user accessed which vault item, and when) without recording what was in those items. The metadata of an event is not the same as the plaintext of the vault entry. Admins get the visibility they need; the content remains encrypted.
4. Client credentials at agencies
For agencies specifically, zero-knowledge carries a client trust implication that goes beyond internal security. When client credentials are stored in a shared team vault, a properly implemented ZK model means those credentials are private even from the agency’s own infrastructure team. If your cloud hosting provider, your DevOps contractor, or a senior employee were to access the server, they would find ciphertext. The ZK guarantee is the agency’s assurance to clients that their credentials are not simply trusted to good behaviour, they are protected by design. That is a secure password vault for teams in the fullest sense of the phrase.
Understanding how All Pass Hub handles team sharing at the architecture level changes the conversation from “which password manager has the best interface” to “which password manager’s security model actually holds up when your team is the threat model.” If you are ready to evaluate this for your team, get started with All Pass Hub to see the implementation in practice.
Security Is Stronger When It’s Built for Teams
Zero-knowledge is not just a technical feature. It is the foundation of trust in any modern password manager. It ensures that sensitive data stays private, even from the provider itself, and reduces the risk surface in the event of a breach. As more teams move toward shared digital environments, understanding how zero-knowledge works in practice becomes essential.
Solutions like Bitwarden demonstrate how strong encryption and transparent security practices can protect individual users and smaller setups effectively. However, as soon as password management becomes a team responsibility, the requirements shift. Secure sharing, access control, and user lifecycle management become just as important as encryption itself.
This is where All Pass Hub stands out. It applies the zero-knowledge principle in a way that aligns with real-world team workflows. By combining strong encryption with a team-first architecture, it enables organisations to share credentials securely, manage access with clarity, and scale without adding operational complexity.
If your use case involves multiple users, ongoing onboarding and offboarding, or frequent credential sharing, choosing a solution built specifically for teams can make a meaningful difference. All Pass Hub offers that balance of security and usability, making it a practical option for teams that want to stay protected without slowing down their operations.
Frequently asked questions
What is zero-knowledge in a password manager?
A zero-knowledge password manager encrypts your vault on your own device before any data is sent to the provider’s servers. The provider stores only encrypted ciphertext and never your master password or decryption key. Even the company’s own engineers cannot read your stored credentials. All Pass Hub uses this model: encryption and decryption happen client-side, and the server receives only data it cannot interpret.
Which password managers are truly zero-knowledge?
Password managers with documented client-side encryption and no server-side key access include All Pass Hub, Bitwarden, 1Password, and NordPass. Each encrypts vault data before it leaves your device and does not store your master password. All Pass Hub additionally uses RSA-based key exchange to preserve zero-knowledge during team credential sharing. Buyers should confirm whether their chosen tool also encrypts vault URLs and metadata, as some providers retain these unencrypted.
What encryption does All Pass Hub use?
All Pass Hub uses AES-128 encryption for vault data, PBKDF2-SHA256 with 600,000 iterations for key derivation from your master password, and RSA-based key exchange for shared team vaults. All encryption and decryption occur client-side; the All Pass Hub server receives only ciphertext that cannot be decrypted without your master password.
Does zero-knowledge mean the company can’t access my passwords?
Yes, in a properly implemented zero-knowledge model, the company cannot access your vault contents even if legally compelled to produce them, because they do not hold your encryption key. However, zero-knowledge does not protect against a compromised device, a weak master password, or metadata the provider may retain (such as login timestamps or unencrypted URLs). Always verify what a provider’s zero-knowledge claim specifically covers.
Can a zero-knowledge password manager recover my account if I forget my master password?
Because a zero-knowledge password manager does not store your master password, the company cannot reset your vault on your behalf. Most implementations offer an emergency access kit or recovery code generated at account creation, this must be stored securely offline. All Pass Hub users should generate and store their recovery code when setting up their account.
